This blog describes how to install Ivanti Automation Dispatcher and Agent on Windows Server Core editions. The Ivanti Automation Admin Guide describes Windows Server Core edition can be used. Because the Core edition doesn’t have the Desktop Experience, it’s impossible to install the Ivanti Automation Console on the Windows Server Core edition.
Only Ivanti Automation Dispatcher and Agent can be installed on a Windows Server Core server.
Use this link to install and configure a Windows Server Core Edition server.
Before we can install the Ivanti Automation products, we need to configure the Windows Firewall, which is enabled by default. There are two options available.
- Disable the Windows Firewall for profiles Domain and Private.
- Add the required ports to the Windows Firewall for profiles Domain and Private.
When installing the Ivanti Automation components from the Ivanti Automation Console – Topology, the SMB (Server Message Block) protocol is required to connect to the server and execute the installation. According to the Admin Guide, Ivanti Automation uses ports 3162, 3163, and 3165 for communication between the components.
The first option is disabling the Windows Firewall for the profiles Domain and Private. When the SConfig isn’t disabled with the command:
Set-SCconfig -AutoLaunch $falsePress 15 and <enter> in the SConfig menu. This closes the SConfig and shows the Command Line PowerShell window.
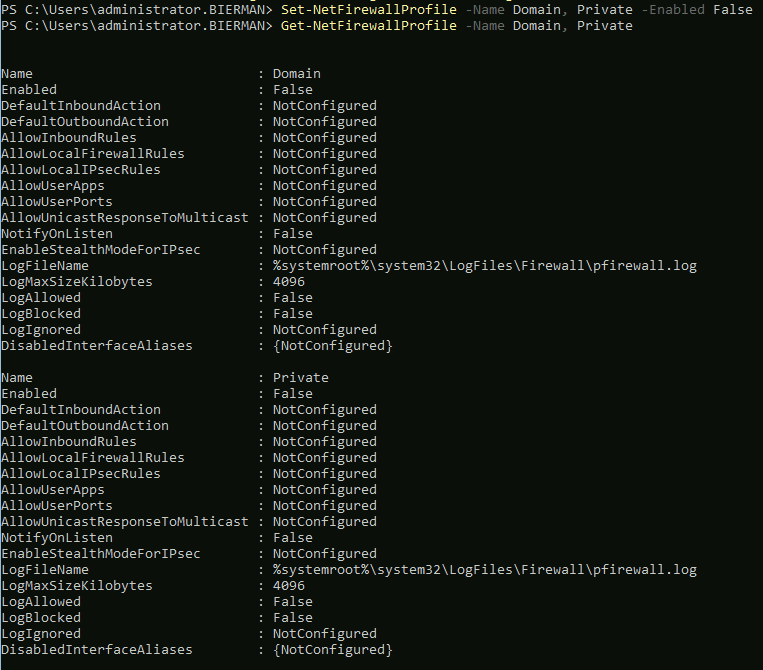
Use the PowerShell command to disable the Windows Firewall for the profiles Domain and Private.
Set-NetFirewalProfile -Name Domain, Private -Enabled FalseUse the PowerShell command below to test if the Windows Firewall profiles are disabled.
Get-NetFirewallProfile -Name Domain, PrivateThis shows if the Windows Firewall profiles are disabled.
The next step is enabling the ports (TCP 445, 3162, 3163, and 3165) and enabling the Windows Firewall profiles. The Ivanti Automation ports (3162, 3163, and 3165) need to be added for Inbound and Outbound. SMB protocol (445) is only needed for Inbound. Execute the following PowerShell commands to add the ports needed to the Windows Firewall profiles.
New-NetFirewallRule -DisplayName ‘Ivanti Automation’ -Profile @(‘Domain’, ‘Private’) -Direction Inbound -Action Allow -Protocol TCP -LocalPort @(‘445’, ‘3162’, ‘3163’, ‘3165’)New-NetFirewallRule -DisplayName ‘Ivanti Automation’ -Profile @(‘Domain’, ‘Private’) -Direction Outbound -Action Allow -Protocol TCP -LocalPort @(‘3162’, ‘3163’, ‘3165’)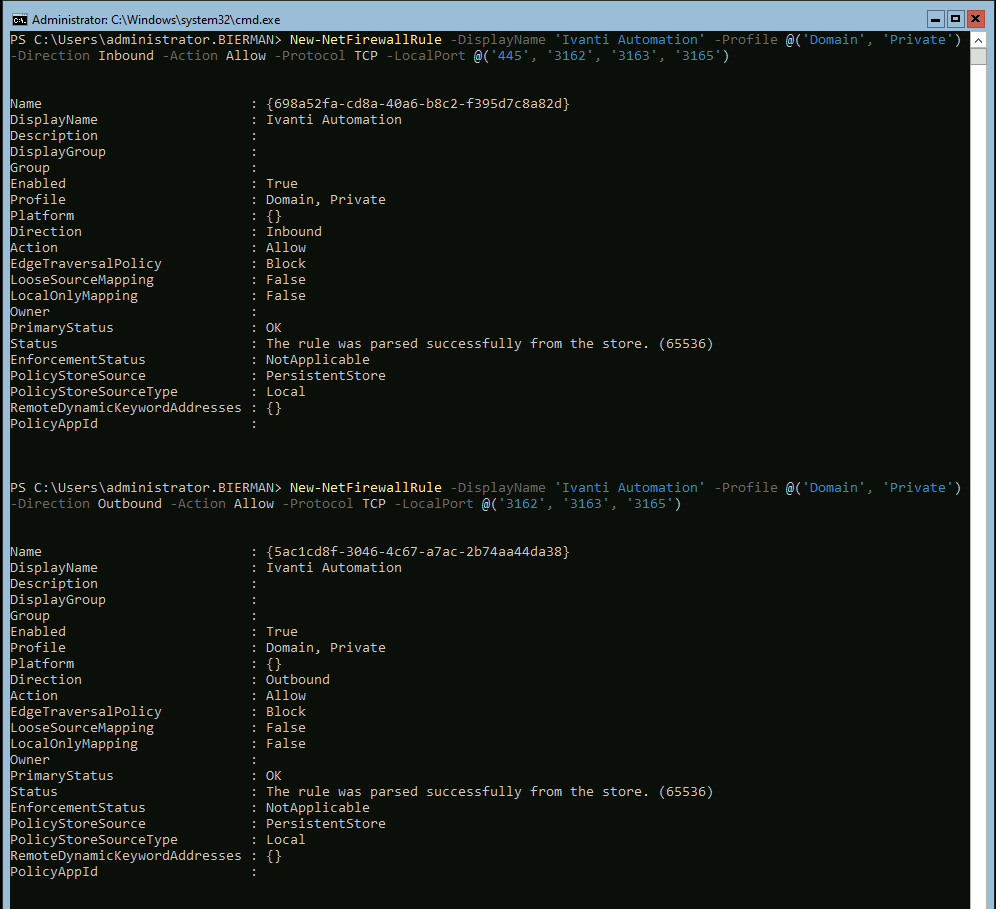
The next step is installing the Ivanti Automation Dispatcher and Agent components on the Windows Server Core edition.
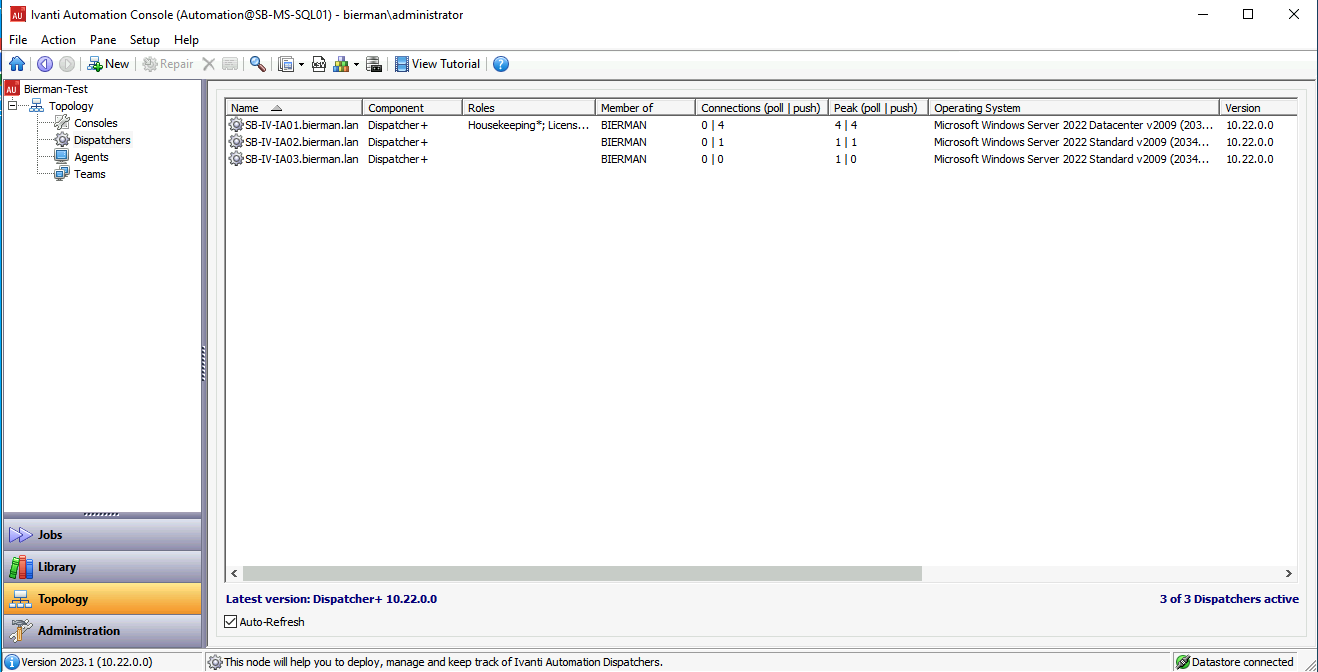
Open the Ivanti Automation Console from a device that has the component installed. Go to Topology – Dispatcher.
Select New from the top menu bar.
Enter the name of the server built.
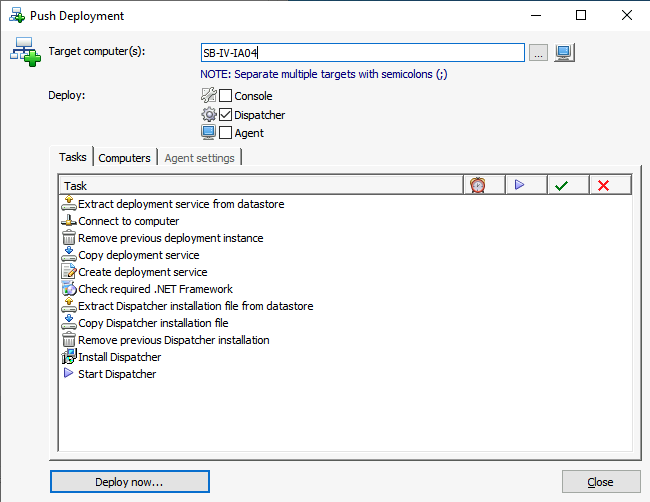
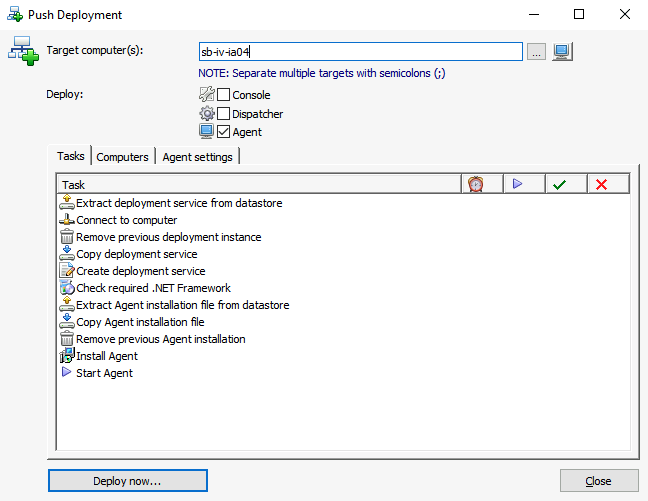
In this blog, we install the components separately to show how the Push Deployments operate.
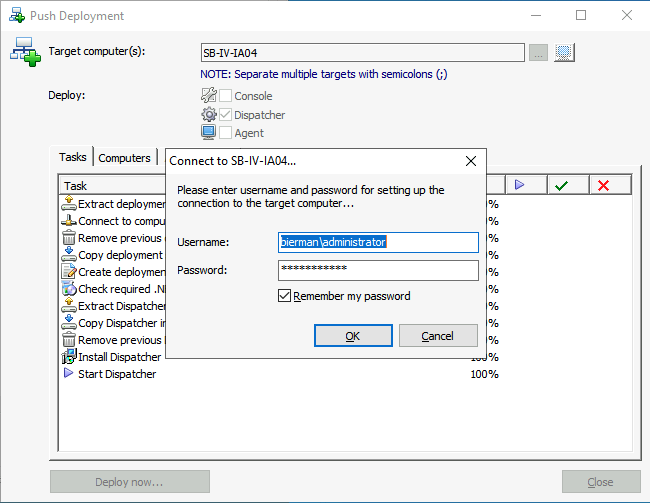
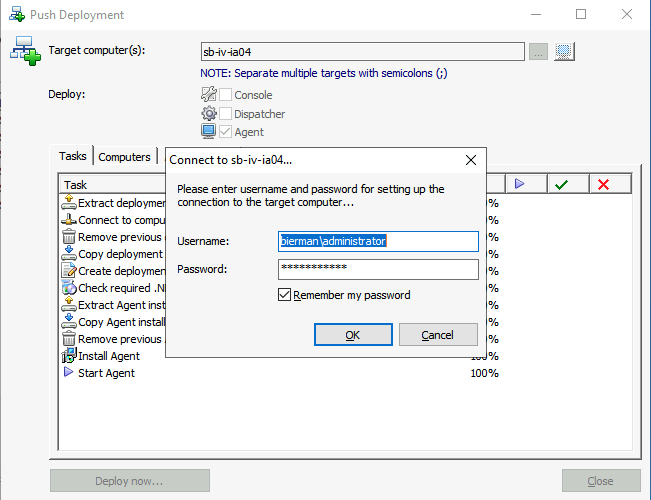
Select Deploy now… to start the installation. Enter a domain username and password which is allowed to connect to server and to install software.
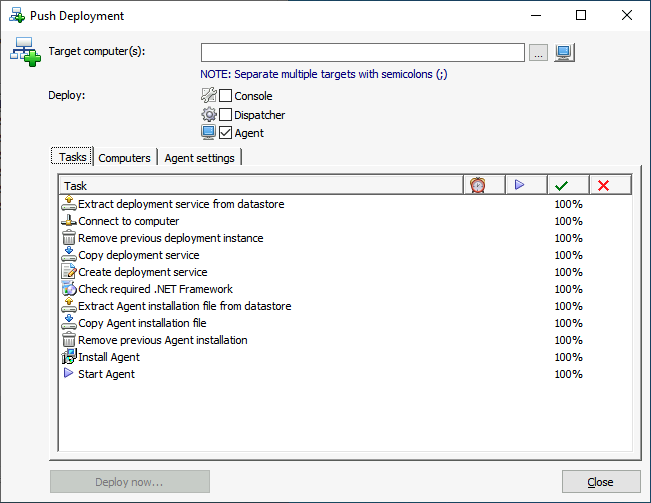
When the installation is successfully finished, all actions have 100% below the green check mark.
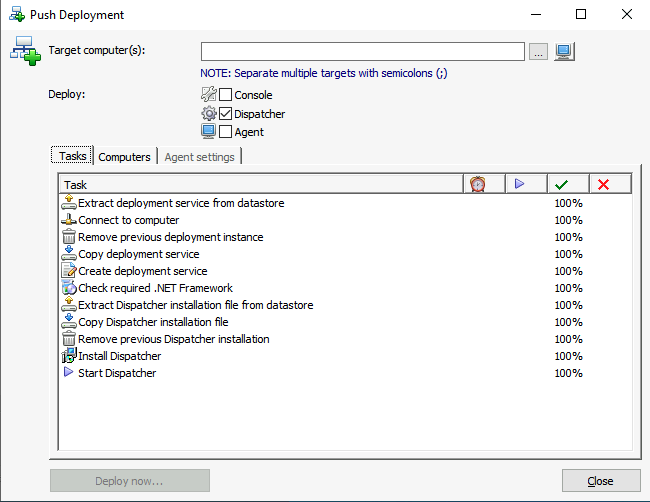
Close the Push Deployment screen. The newly added/installed Dispatcher is added to the Dispatcher list.
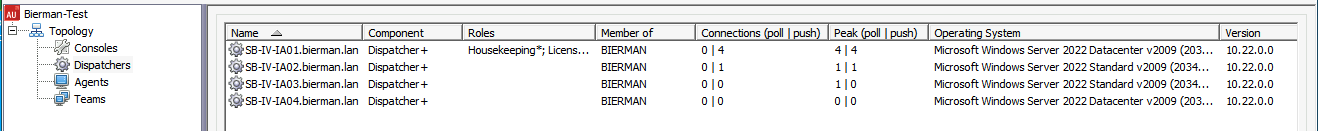
In the Ivanti Automation Console, select Setup – Global Settings – Dispatcher Detection – Dispatcher discovery. Make sure the newly installed Ivanti Automation Dispatcher is added to the list.
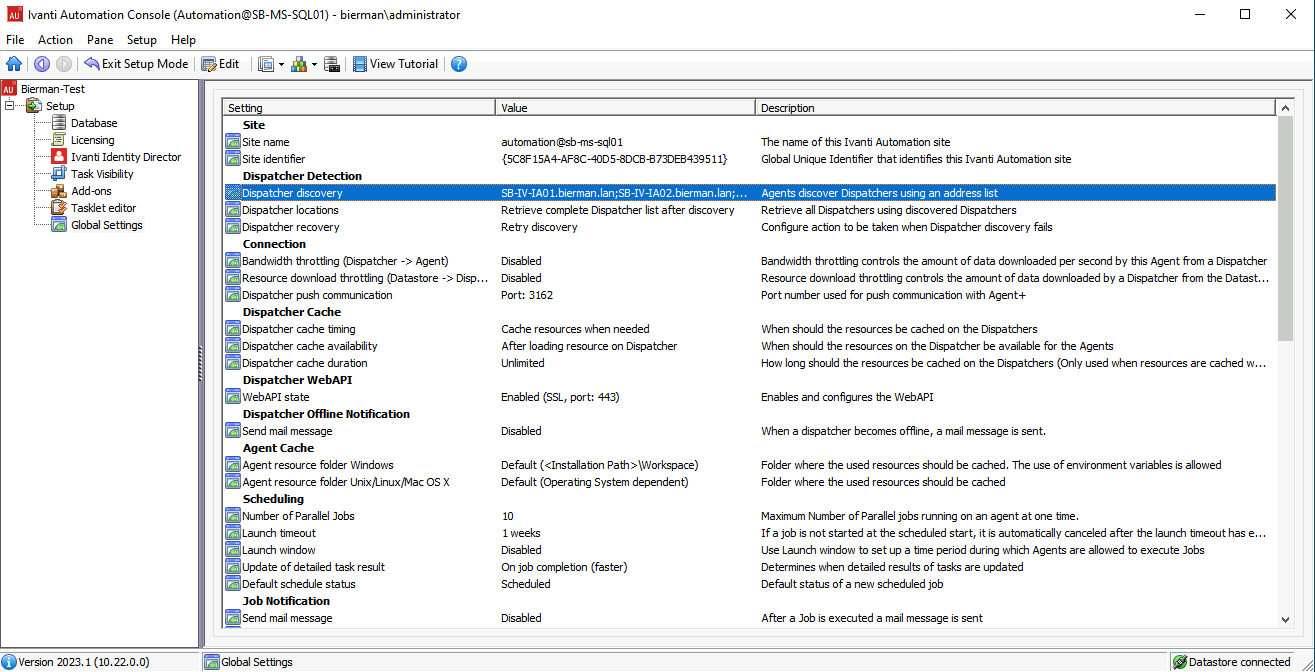
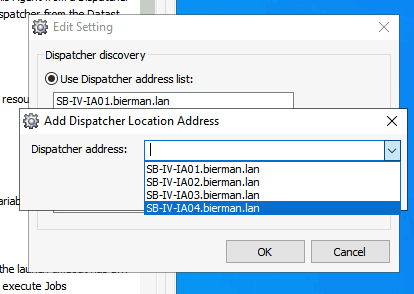
When no Ivanti Automation Dispatchers are added to this Global Setting, the installed Agent will not be shown in the Agent overview because it can’t connect to the Ivanti Automation Dispatcher(s).
The setting is required for Push Deployment or manual installation.
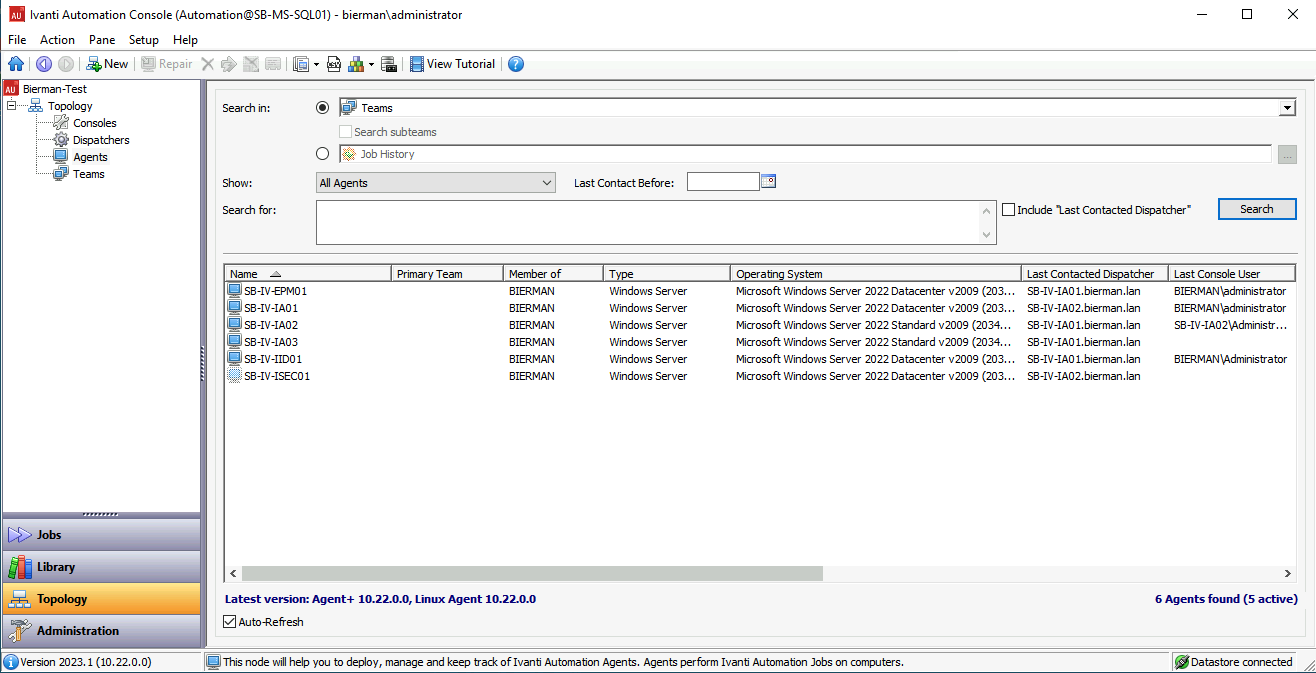
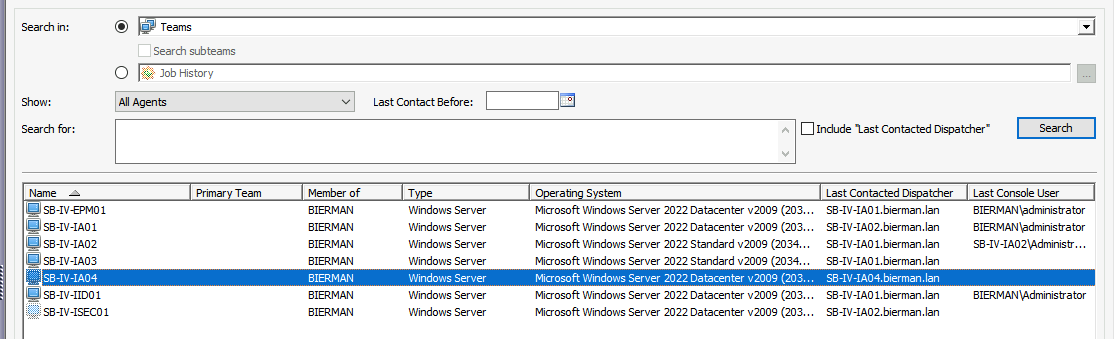
For the installation of the agent, the Push Deployment is equal to the installation of the Dispatcher. Only select Agents from the Topology. New Agents are not automatically shown in the overview. Select Search to resolve all Agents installed.
See the screenshots below for the Ivanti Automation Agent push deployment.
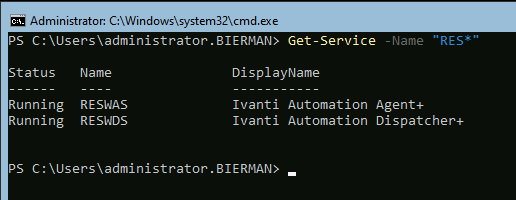
Use the PowerShell command below to check if both Ivanti Automation services are running.
Get-Service -Name “RES*”